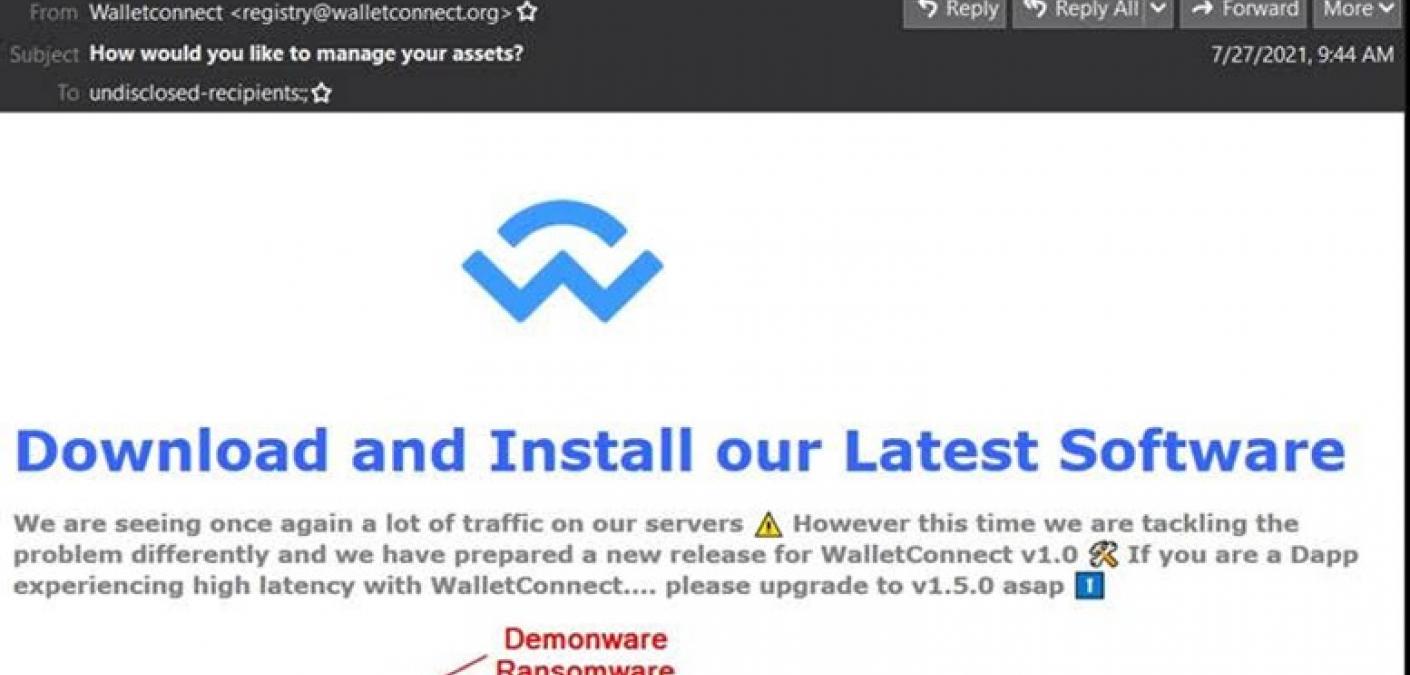
Microsoft-Themed Email Campaigns Using CodeSandbox, IBM Cloud to Host Phishing Sites
Microsoft-Themed Email Campaigns Using CodeSandbox, IBM Cloud to Host Phishing Sites
Digital attackers are using Microsoft-themed attacks emails to redirect victims to phishing sites hosted on CodeSandbox and IBM Cloud.
Read more