Oski Infostealer Delivered by Fake Payment Slip Emails

Phishers leveraged fake payment slip emails to target unsuspecting users with samples of the Oski infostealer.
Check Your Bank Details…so that Oski Can Steal Them
In mid-August, the Zix | AppRiver team flagged an attack email that arrived with the subject line “Payment Slip.”
The body of the message informed the recipient that the email came with an attached payment document. It then made a grammatical error by instructing the recipient to “open the document and check if your bank details is correct. [sic]”
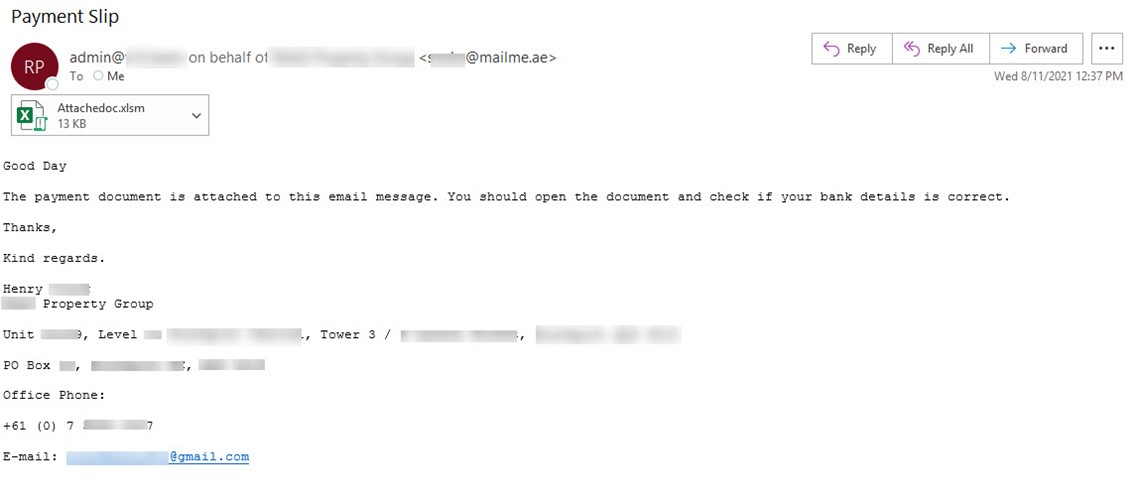
To add a sense of legitimacy, the email’s creators added a signature block that included the name, office phone number, and email address for someone named “Henry” working at a company based in Australia.
This isn’t the first time that Zix | AppRiver has detected a payment-themed phishing campaign.
Back in mid-July, for example, the firm’s security researchers came across a phishing campaign that used a concise Request for Payment lure to trick a recipient into opening a .XZ document.
Clicking on the file revealed an executable file that came packed with a bingo game as a means of evading detection and distributing AgentTesla as its final malware payload.
A Look at Oski Infostealer
The attack email in the phishing operation identified above arrived with an Excel document named “Attachedoc.xlsm.”
When opened, the document loaded malicious macro code to infect the recipient’s machine with the Oski infostealer.
News of Oski first emerged in early 2020 after a security researcher named Aditya K. Sood uncovered advertisements for the malware on dark web forums, reported Threatpost.
Sood and his team decided to investigate further, so they used brute-force tactics to compromise the malware’s web-based PHP command-and-control server (C2) located in Russia.
In doing so, the security team learned that Oski had started out targeting victims in North America but had then added China to its list of targeted geographies.
The malware leveraged DLL injection to hook into a victim’s browser processes so that it could conduct a Man-in-the-Middle (MitM) attack, enabling Oski to target users’ credentials saved in more than 20 web browsers.
The threat also stole credentials from registry, passwords in the infected machine’s SQLite database, and session cookies stored for cryptocurrency wallets and other accounts.
It did this all without obtaining explicit administrative privileges and by coming wrapped under a wrapper payload that self-destructed when Oski successfully loaded into a system.
Taken together, these tactics helped the malware to evade detection by traditional antivirus solutions so that it could successfully exfiltrate a victim’s credentials.
Oski isn’t the first infostealer ever detected by Zix | AppRiver.
Back in early 2020, for instance, the firm spotted a campaign that used PowerPoint to infect recipients with the Lokibot infostealer and the AZORult remote access trojan.
It was around the same time when security researchers detected a campaign that used COVID-19 stimulus as a lure to deliver Remcos, a remote access trojan which then followed up with a Formbook info-stealer infection.
More than a year later, Zix | AppRiver observed a fake Moneycorp email that distributed information-stealing malware known as AveMaria.
Defending Against Email-Borne Infostealers
Organizations can defend themselves against email-borne infostealers by investing in an email security solution that’s capable of scanning incoming messages for campaign patterns, IP addresses, malware signatures, and other threat indicators. That analysis should occur in real time so that legitimate business correspondence can reach its intended destination.
