 3 Recent Attacks Where Phishers Abused Google’s Services
3 Recent Attacks Where Phishers Abused Google’s Services
Read about 3 recent cyber attacks where Google was leveraged and abused - and get prepared for upcoming threats around new Google 2FA requirement.
Read more 3 Recent Attacks Where Phishers Abused Google’s Services
3 Recent Attacks Where Phishers Abused Google’s Services
Read about 3 recent cyber attacks where Google was leveraged and abused - and get prepared for upcoming threats around new Google 2FA requirement.
Read more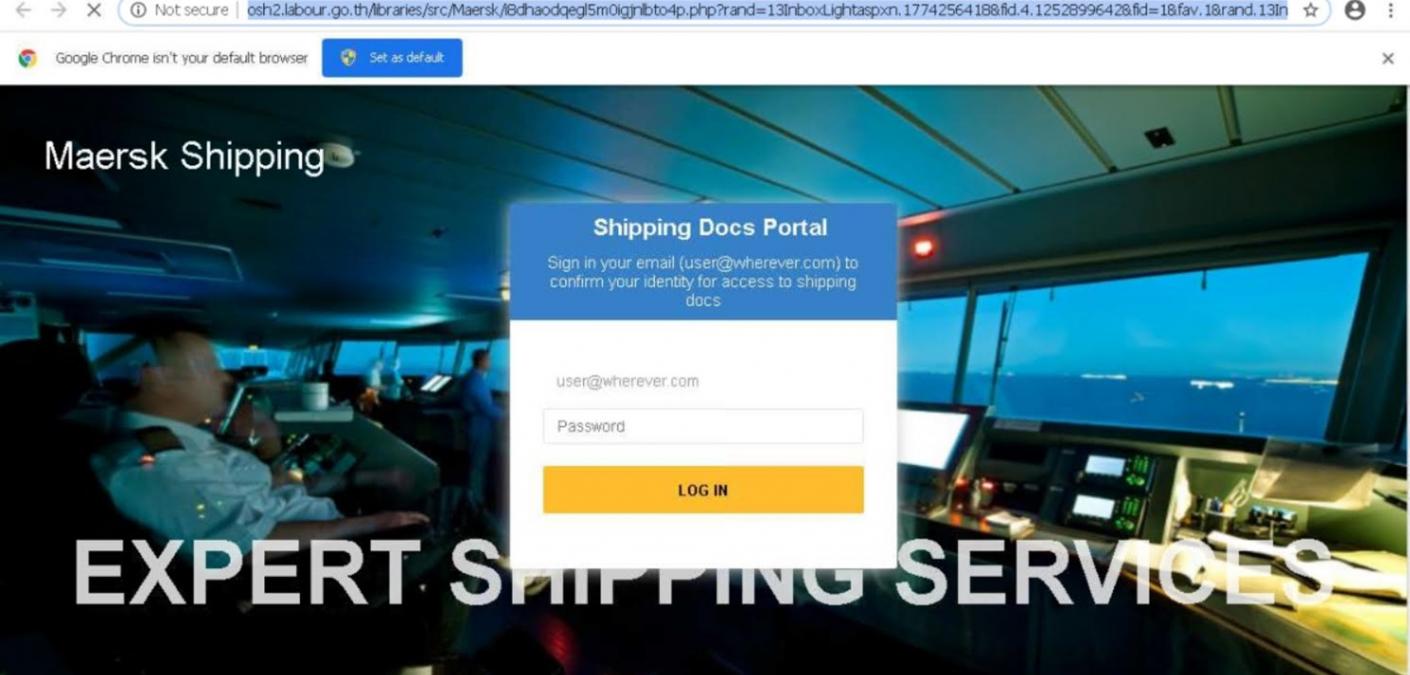 Phishers Impersonating Maersk Line to Steal Victims’ Email Credentials
Phishers Impersonating Maersk Line to Steal Victims’ Email Credentials
Phishers launched an attack campaign impersonating Danish international container shipping company Maersk Line to steal victims’ email account credentials.
Read more Where I Go, So Does Zix: Securing Private Healthcare Facilities with Hands-Free Email Threat Protection
Where I Go, So Does Zix: Securing Private Healthcare Facilities with Hands-Free Email Threat Protection
In this case study, a small healthcare business IT leader talks about her trust in Zix email threat protection for to fill security gaps with simplicity.
Read more 5 Types of Phishing and How To Spot Them A Mile Away
5 Types of Phishing and How To Spot Them A Mile Away
Learn what different types of phishing attacks can look like and how to help your team avoid falling for them.
Read more What Does Encrypted Email Really Mean?
What Does Encrypted Email Really Mean?
If you want your email to be secure, then adopting encrypted email practices is critical.
Read more What Is Spoofing and Does My Team Need To Be Concerned?
What Is Spoofing and Does My Team Need To Be Concerned?
Spoofing is the insidious act of disguising a communication from an unknown source as being from a known, trusted source.
Read more Bringing Large File Share to Zix Email Encryption Users Everywhere
Bringing Large File Share to Zix Email Encryption Users Everywhere
Zix introduces Secure Large File as part of email encryption service, improving collaboration as any authorized user can send large attachments from their email.
Read more Understanding Digital Attackers’ Appropriation of the “As a Service” Model
Understanding Digital Attackers’ Appropriation of the “As a Service” Model
Recently, I wrote about Microsoft’s discovery of a new phishing-as-a-service (PhaaS) offering called “BulletProofLink.” PhaaS functions similarly to
Read more What is Ransomware, How to Prevent It, and How to Respond If You're Attacked
What is Ransomware, How to Prevent It, and How to Respond If You're Attacked
What is ransomware? This blog tells you what it looks like, how to avoid it, and ways to recover.
Read more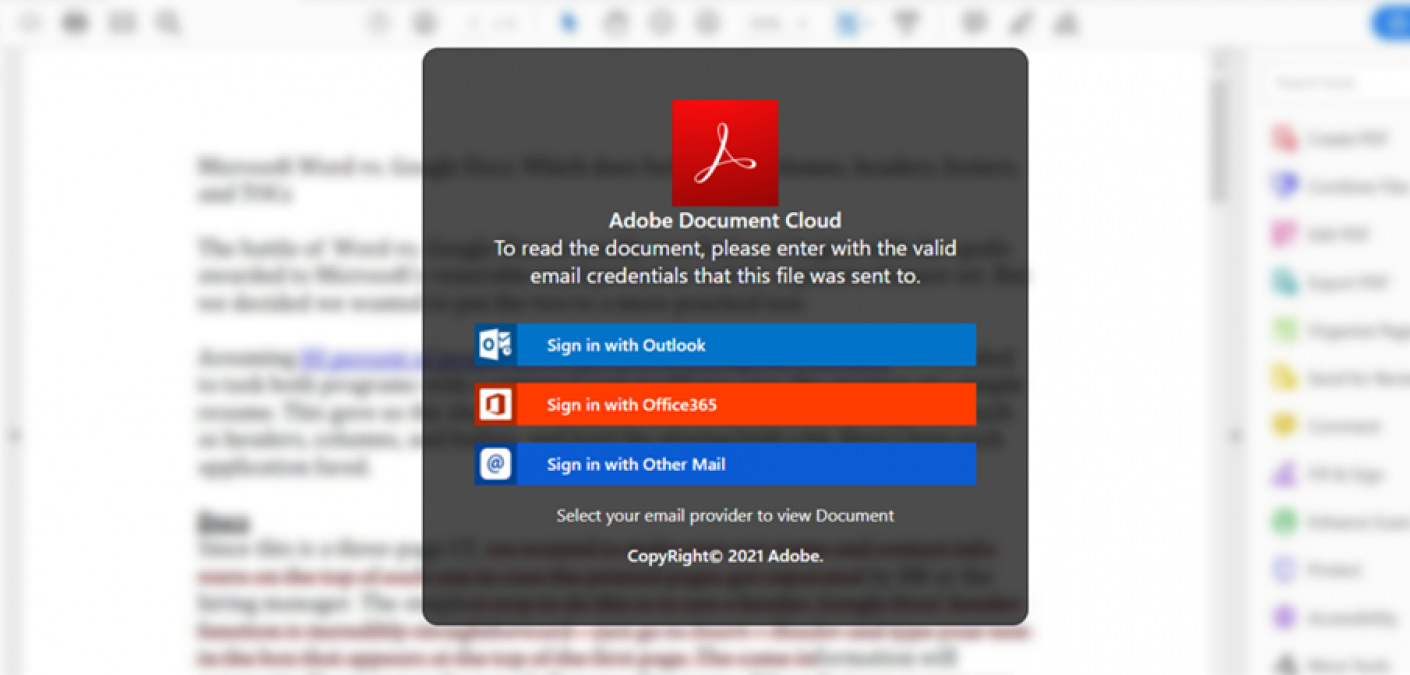 DocuSign Abused by Phishers to Target Victims’ Email Account Credentials
DocuSign Abused by Phishers to Target Victims’ Email Account Credentials
Digital attackers launched a phishing campaign in which they abused DocuSign to steal victims’ email account credentials.
Read more