Blog
 How Finance and Insurance Providers Can Respond To The Surge of Cyberattacks
How Finance and Insurance Providers Can Respond To The Surge of Cyberattacks
How has WFH altered the digital landscape and what can both financial and insurance providers do to respond to this increased growth?
Read more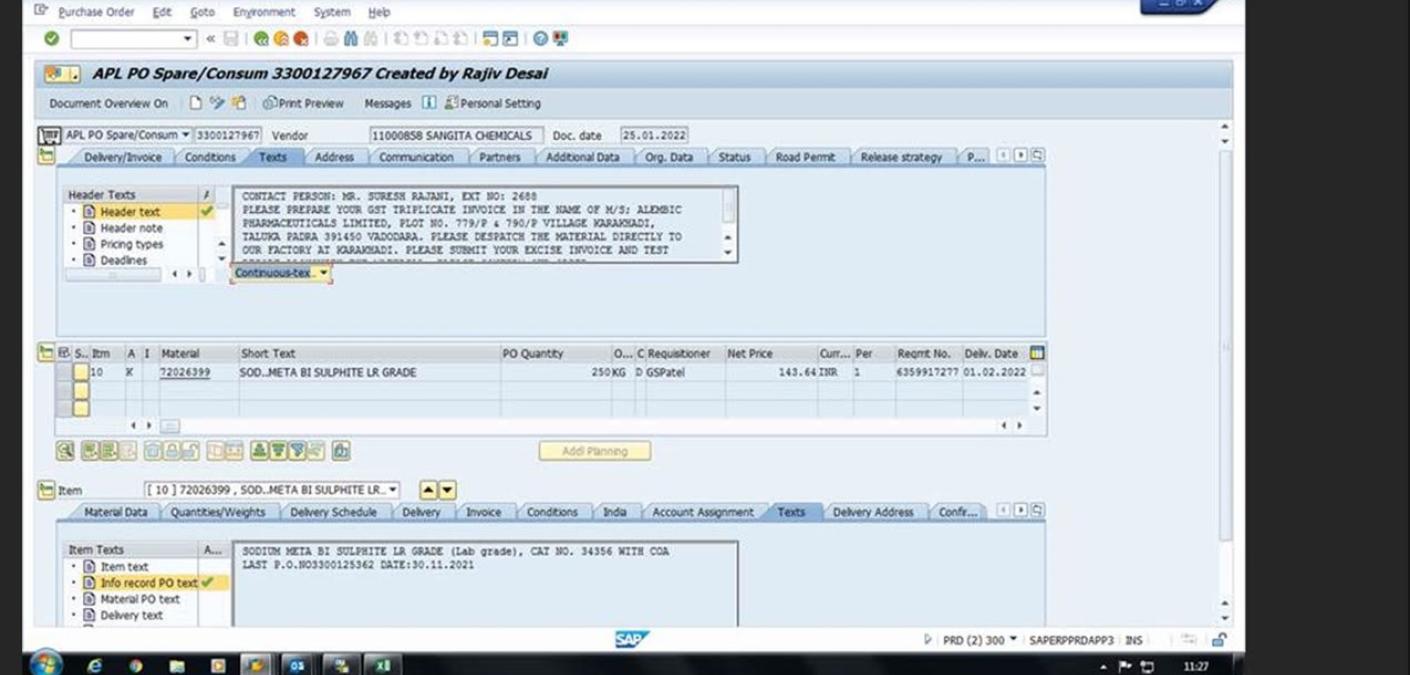 Formbook Loader Distributed in Three “Extremely Aggressive” Email Attacks
Formbook Loader Distributed in Three “Extremely Aggressive” Email Attacks
Malicious actors launched three “extremely aggressive” email attacks in which they attempted to distribute samples of the Formbook loader.
Read more 10 IT Trends for 2022 that MSPs should know
10 IT Trends for 2022 that MSPs should know
While many businesses have been taking a reactive approach to IT changes, 2022 is ushering in a new era. Here are IT 10 trends CompTIA predicts for 2022.
Read more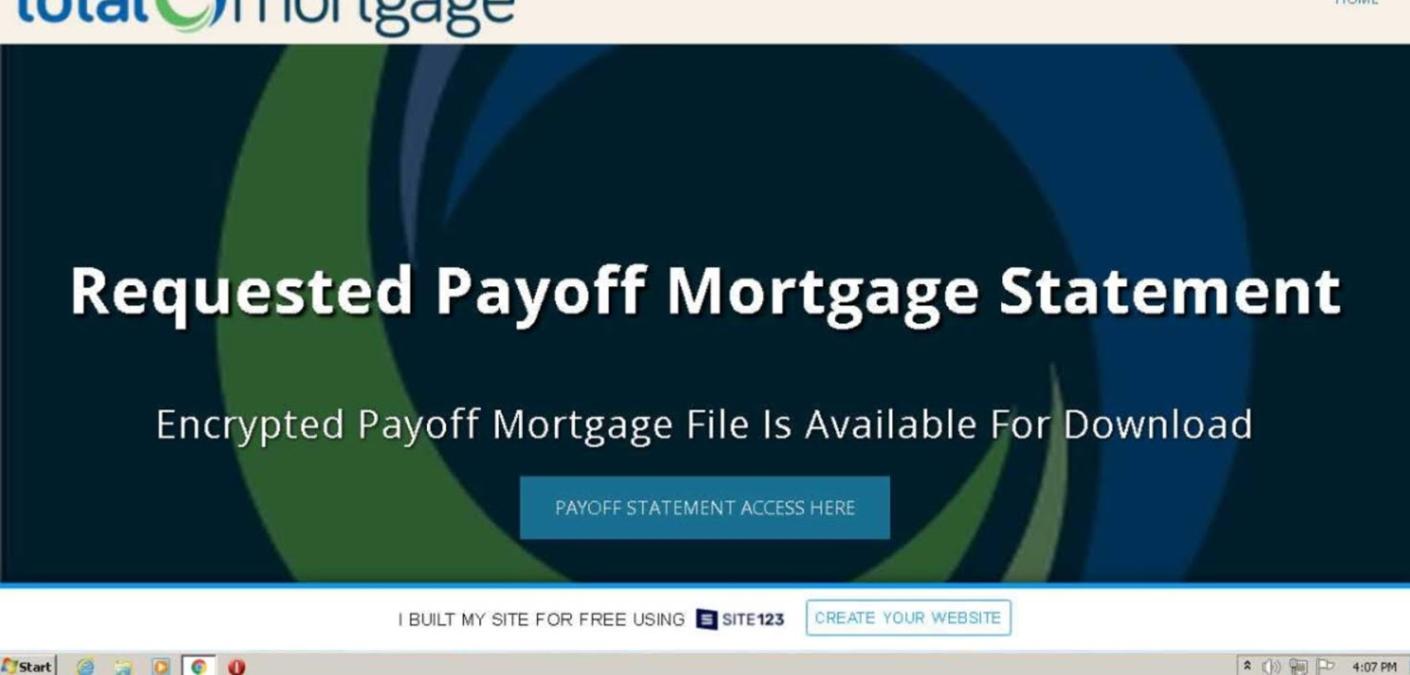 Attackers Targeting Mortgage Servicers to Steal Email Accounts Credentials
Attackers Targeting Mortgage Servicers to Steal Email Accounts Credentials
Digital attackers are targeting mortgage servicers and their clients to try to steal victims’ email account credentials.
Read more 6.5 Billion Emails Quarantined in 2021
6.5 Billion Emails Quarantined in 2021
The Zix | AppRiver team quarantined 6.5 billion emails in 2021, a volume which constituted a 12.5% increase over the previous year.
Read more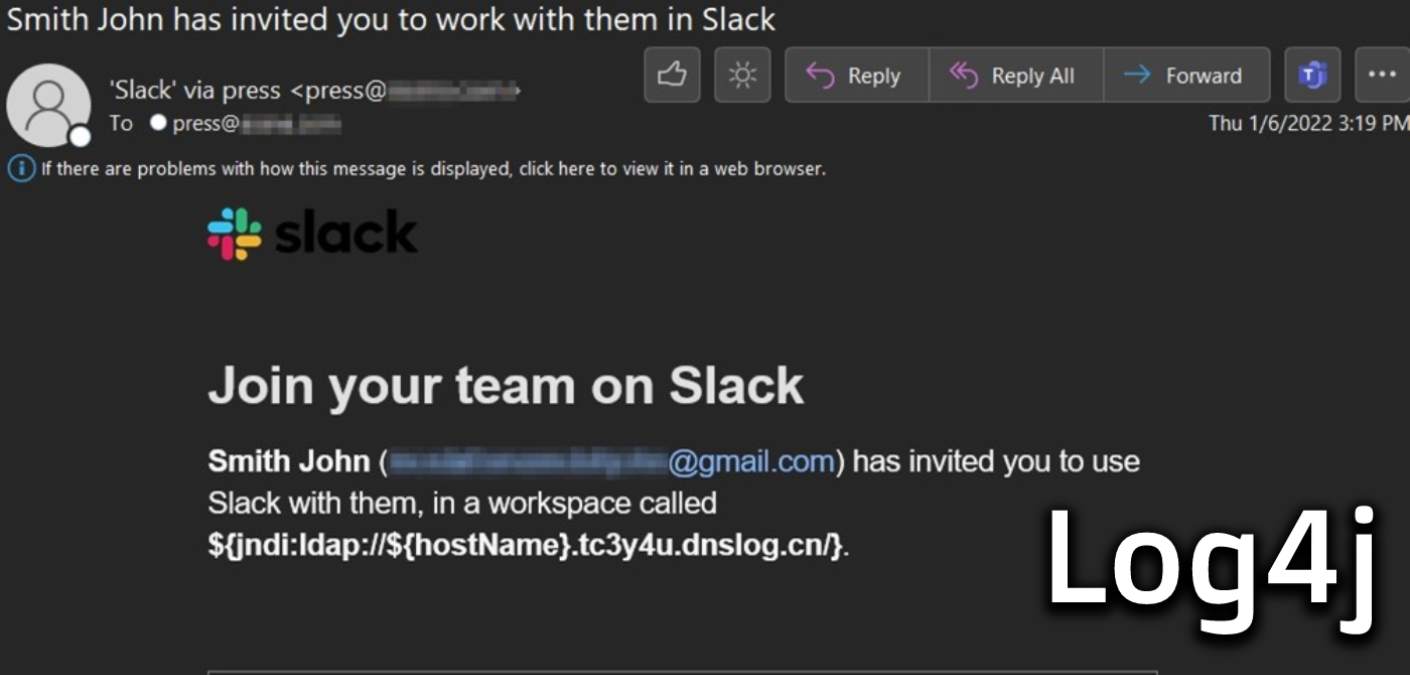 Log4Shell Targeted by Email Attackers in Two Campaigns
Log4Shell Targeted by Email Attackers in Two Campaigns
The Zix | AppRiver team spotted two campaigns in which email attackers attempted to exploit a recently disclosed Log4j vulnerability on susceptible systems.
Read more 4 of the best Microsoft Teams features you may not be using today
4 of the best Microsoft Teams features you may not be using today
There’s more to Microsoft Teams than video meetings, instant messages, and project channels. We look at 4 features that can help your team work smarter together.
Read more Advanced Notice: Staying Alert and Aware of a Security Breach
Advanced Notice: Staying Alert and Aware of a Security Breach
Knowing if you’re in the midst of a data breach isn’t always obvious. What signs do you need to be vigilant of?
Read more How to increase adoption of Microsoft Teams
How to increase adoption of Microsoft Teams
Microsoft Teams is a powerful hub for the modern workplace - but it's often underused. How can you encourage more meaningful adoption of Teams at your workplace?
Read more Data Resilience 101
Data Resilience 101
What does "data resilience" mean? It's a backup plan for your organization's most important data. In this article, MSP CTO explains the importance of resilience.
Read more IP Spoofing Attacks: What are they and how can you prevent them?
IP Spoofing Attacks: What are they and how can you prevent them?
Learn what IP spoofing attacks are, why they’re sneaky and insidious, and how to avoid them.
Read more A rundown of backup recovery and data loss
A rundown of backup recovery and data loss
Data loss can be catastrophic for an organization. In order to best be prepared, it’s critical to have a robust backup recovery in place.
Read more



