Can you send large files via email – and without security risk?

Take a second and think about how your employees or clients are sending large files today.
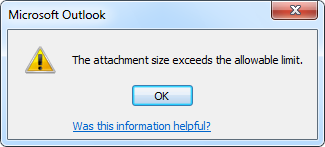
Are they limited by the size requirements in email – their preferred way of communicating? Probably.
Are they then sharing these important, secure files in person by bringing a USB to the intended recipient? Given the current work-from-home-we-are-in-a-pandemic environment, probably not (and this likely wasn’t their workflow prior to having a home office).
Are they instead using a (maybe unauthorized) but simple and convenient file sharing platform that is a part of their current workflow (like Google Drive, a personal file sharing account like Box or just sending the files over Zoom chat)? Most likely.
So what does this mean for you as the IT leader or partner driving productivity, security and compliance? More headaches, more time spent fielding requests on how to send large files, more time worrying about unintentional data loss (because the tools aren’t there to prevent it) or more time setting your users up on yet another platform to facilitate file sharing. All while considering how to maintain compliance policies across all these platforms.
Not so anymore. With the introduction of Zix Secure Large File, you can make sharing large files securely as easy as hitting send.
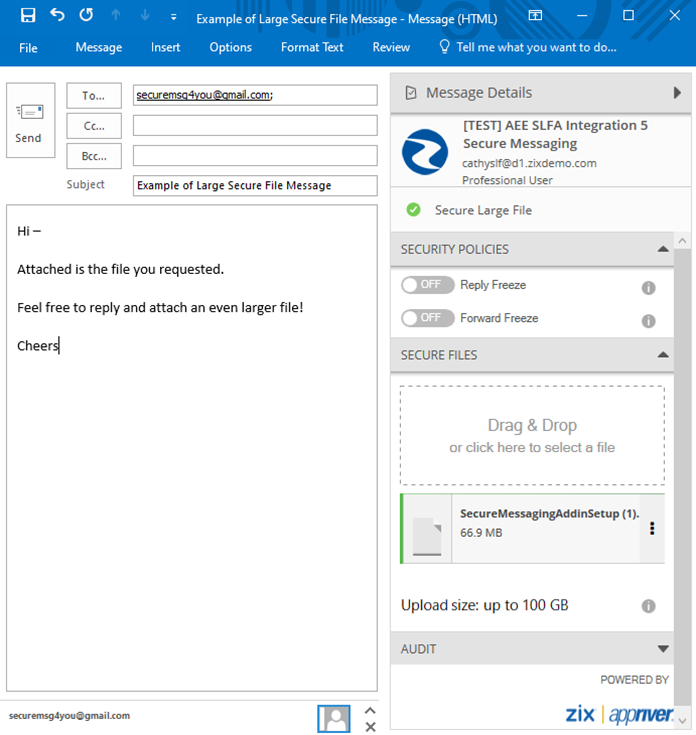
Senders can send any file type, up to 100 GB per message, with no storage quotas. Messages are received through your current custom-branded Secure Messaging Portal, appearing just like any other encrypted email to your recipients. Your recipients, by the way, have nothing new to learn. There is no difference between receiving a Zix Encrypted Email or a Zix Secure Large File email. And they can also send large files by responding to your original message or logging into your portal at any time and composing a message.
So now the patient financial data between the billing department and insurance company isn’t in a shared Google Drive account. And the revenue data sent between sales and marketing leaders is no longer in a Zoom chat or living in a personal Shadow IT tool the user downloaded on their own. And you and your team can rest easy knowing users are empowered, security is activated and regulations are met.
Less of this,
More of this,