Blog
 Phishing Attack Packs Executable File with Bingo Game to Distribute AgentTesla
Phishing Attack Packs Executable File with Bingo Game to Distribute AgentTesla
A phishing campaign packed an executable file together with a bingo game to distribute AgentTesla as its final malware payload.
Read moreThe 2021 mid-year threat report is now available. This blog highlights what stands out from the report - highly sophisticated email attacks.
Read more Lockers vs. Crypto-Malware: How These Two Ransomware Categories Stack Up
Lockers vs. Crypto-Malware: How These Two Ransomware Categories Stack Up
Crypto-ransomware threats are the most familiar ransomware subcategory, but how do they differ from locker threats - another prevalent ransomware type?
Read more RaaS: What Is It and Why Is It Making Ransomware More Prevalent?
RaaS: What Is It and Why Is It Making Ransomware More Prevalent?
Organizations must defend themselves against Ransomware-as-a-Service (RaaS), where malware authors franchise ransomware to affiliates for a cut of the profit.
Read more NFTs – How Safe Are They?
NFTs – How Safe Are They?
NFTs are all the rage at the moment, but how safe are they? Learn about all the potential NFT security risks right here.
Read more BitRAT Distributed by Phishing Emails Disguised as RFQ Notices
BitRAT Distributed by Phishing Emails Disguised as RFQ Notices
Phishers are using Request For Quote (RFQ)-themed emails to infect users with BitRAT.
Read more Ransomware on the Rise
Ransomware on the Rise
Ransomware cripples the target company’s operations, making it much different from an attack that steals data. The implication of this became clear as I developed a contingency plan to pay a ransom. Before thinking through the issue, I pictured the payment as a get-out-of-jail
Read more 7 Top Delivery Vectors for Ransomware
7 Top Delivery Vectors for Ransomware
In 2020, ransomware attacks increased by 485% compared to 2019. The majority (64%) of those attacks took place in the first two quarters of the year, reported Infosecurity Magazine.
Read more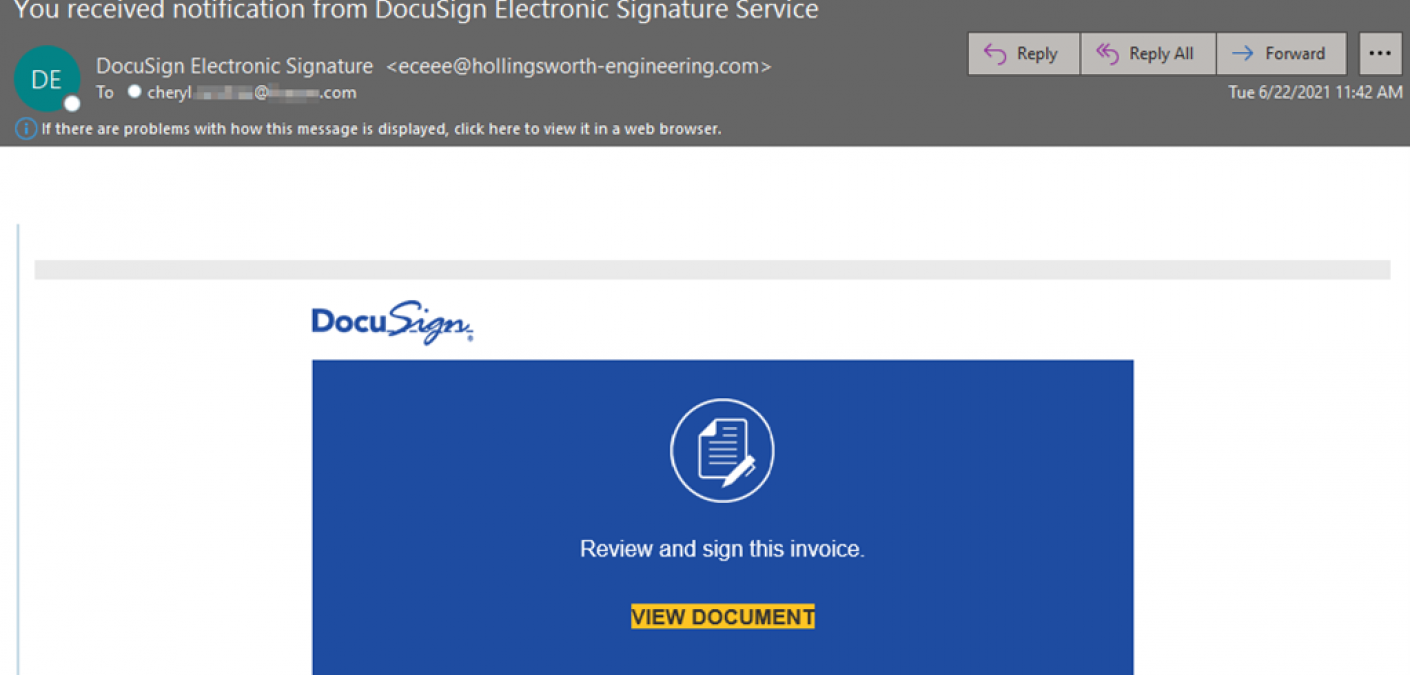 Phishers Misusing Feedburner Links to Redirect Users to Phishing Pages
Phishers Misusing Feedburner Links to Redirect Users to Phishing Pages
Email attackers are leveraging Feedburner links to redirect recipients to phishing pages.
Read more Understanding the Connection between Ransomware and Email
Understanding the Connection between Ransomware and Email
Email is one of the most common delivery vectors employed by ransomware attackers today.
Read more REvil Ransomware Gang Demands $70M in Kaseya Software Supply Chain Attack
REvil Ransomware Gang Demands $70M in Kaseya Software Supply Chain Attack
The REvil ransomware gang demanded $70 million in a software supply chain attack involving American software company Kaseya.
Read more Malware Distributors Leverage Kaseya Attack
Malware Distributors Leverage Kaseya Attack
Ransomware continues to be a major threat, and just this week one of our own MSPs was hit. Learn more about this recent ransomware episode here.
Read more



