Tech Support Scammers Claim Victims Viewed Adult Content on Their Computers

Zix | AppRiver spotted a tech support scam in which digital fraudsters claimed that victims had viewed adult content on their computers.
Researcher at Zix | AppRiver received an email in mid-June 2020 that claimed to originate from Microsoft Support.
Using the subject line “IP blacklisted,” the email claimed that Microsoft Support had uncovered instances in which the victim had accessed adult content on their computer.
They said that those instances constituted violations of the Information Technology Act of 1996.
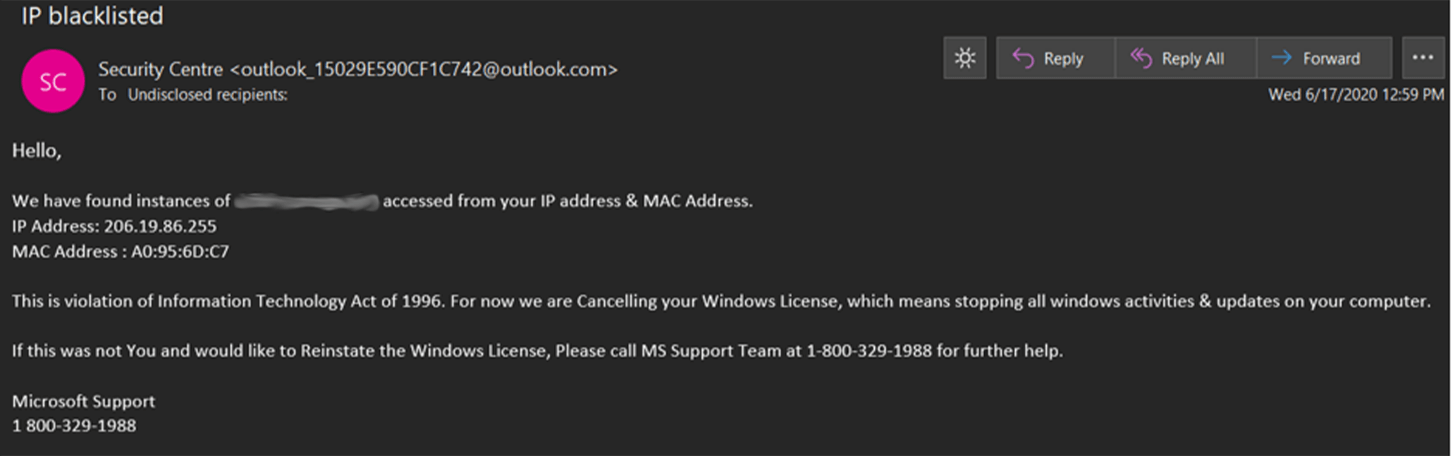
In response, the individuals impersonating Microsoft Support said that they had decided to cancel the victim’s Windows license, thereby “stopping all windows activities & updates on [the victim’s] computer.” They then informed the victim that they could contact Microsoft Support for assistance by calling 1 (800) 329-1988 in the event that there had been a mistake and that they wanted to reinstate their Windows license.
Breaking Down This Hot Mess of a Scam
It’s important to understand just how much this scam got wrong.
Let’s start with the spoofed sender address. The email claimed to originate from Microsoft’s “Security Centre.” To bolster their attack’s credibility, the malicious actor used “outlook_15029E590CF1C742@outlook[dot]com” as their sender address. Perhaps they assumed that they could convince a recipient the message had originated from the Redmond-based tech giant by including the word “outlook” twice in the email address. Despite those hopes, the long alphanumeric string gave this email address away as a fake.
That was only the beginning.
Drilling down into the body of the email, the scammer informed the recipient that they had blacklisted the recipient’s IP address and MAC address. It then named those addresses: “206.19.86.255” and “A0:95:6D:C7.”
At this point in the scam, the attacker clearly made the mistake of assuming that a recipient didn’t know anything about IP addresses or MAC addresses. They therefore didn’t mind overlooking the fact that the MAC address included in the email was incomplete and incorrect. (Not only is it missing its final two octets, but the first three octets do not trace back to any company.) Also, the IP address specifically pertains to users of Motorola Mobility who live in Pennsylvania; no one else would have that specific IP address.
This brings us to the essence of the threat email: the premise that Microsoft cancelled the recipient’s Windows license because they had violated the Information Technology Act of 1996. First, let’s simply note that not everyone receiving this email would have a Windows license to begin with. Someone by the name “Nimrod” made this point clear on an 800Notes posting for the fake Microsoft support number associated with this campaign:
Microsoft does not track peoples web usage and does not cancel a Windows license based on where you go on the web. The scammers are guessing that their intended victim is using Windows since it is the most common OS. Users of Mac OS and Linux merely laugh at such threats.
Nimrod went on to explain that the attacker also got their pieces of legislation wrong. In citing the Information Technology Act of 1996, the malicious actors probably meant the Information Technology Management Act of 1996. This law’s purpose was to improve the means by which the federal government acquired, used and disposed of IT assets. It therefore goes without saying that this Act would have no bearing on what users are viewing on their computers.
Defending Against Tech Support Scam Emails…Even the Poor Ones!
All of the mistakes elucidated above show just how lazy the scammers were in designing this particular attack attempt. Unfortunately, there are email attackers out there who will be much more thorough in crafting their campaigns. In response, organizations should invest in a security solution that can help analyze incoming messages for indicators of attack campaigns while allowing legitimate correspondence to reach their intended destinations.
